

By: Cristopher Provoste
Estimated Reading Time: 10 min.
Many people — and even many technical resources — reduce brute force attacks to “guessing passwords on a login page.” That definition is convenient, but dangerously incomplete.
From an attacker perspective, brute force is not about login forms. It is about persistence through volume. It is the systematic and automated testing of possibilities until something breaks, responds differently, or reveals useful information.
At its core, brute forcing is the ability to send a high volume of varied inputs against one or more functionalities without being blocked, rate-limited, or detected. The target may be passwords, directories, API keys, OTP codes, hashes, usernames, or even hidden endpoints. The principle remains the same: exhaust the search space until a valid condition is discovered.
Brute force is not a single attack. It is a strategy.
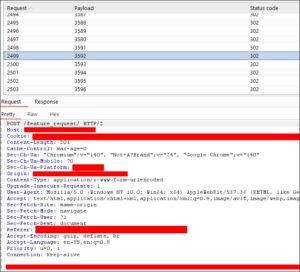
In web applications, an attacker may begin by enumerating available directories in order to discover hidden or unintended resources. This is typically achieved by sending a large number of HTTP requests (GET, POST, etc.) to different paths without being blocked or rate-limited.
In many cases, applications expose hidden directories or files that were not intended to be publicly accessible. These may include files such as /package.json, /installed.json, or other configuration artifacts that reveal framework versions, plugin versions, or dependencies with publicly known vulnerabilities.
Sometimes, directory enumeration can also uncover administrative panels, backup files, development endpoints, or internal paths that were assumed to be inaccessible. All of this becomes possible through brute force techniques based on wordlists (dictionary attacks), where the attacker systematically tests potential paths until valid resources are discovered.

Brute force does not only target authentication mechanisms or hidden directories. In some cases, it can directly impact a company’s operational costs and service availability.
For example, exposed or improperly restricted API keys — such as a Google Maps API key — can be abused by sending a large volume of automated requests. If usage limits are not properly configured, this may lead to excessive billing charges, as the provider bills based on request volume. In extreme cases, once usage quotas are exceeded, the API key may be automatically restricted or disabled, resulting in a denial of service for legitimate users of the application.
(Reference: Google Maps Platform Pricing – https://mapsplatform.google.com/pricing/)
Another common example involves SMTP or email delivery services. Consider an account registration feature that sends a confirmation email to each new user. If this functionality is not rate-limited, an attacker could abuse it by automating account creation requests, flooding the SMTP service with outbound emails. This can lead to increased operational costs, potential account suspension by the email provider, and degraded application performance. In severe cases, it may result in a temporary denial of service affecting legitimate users.
In both scenarios, brute force is not used to guess credentials, but rather to exhaust resources — financial, computational, or service-based.
No. While they may appear similar — since both can involve sending a large number of requests — there are key differences between them.
A Denial of Service (DoS) attack is primarily a resource exhaustion attack. It typically targets network bandwidth, server capacity, or system resources by overwhelming a host or service with a high volume of traffic, often consisting of large numbers of packets or requests. The goal is to make the service unavailable to legitimate users.
On the other hand, brute force attacks target functionality rather than infrastructure. Instead of simply flooding a system, brute force abuses a specific feature or parameter — such as a login endpoint, an ID value, a token, a directory path, or an API function. The objective is not necessarily to take the service offline, but to systematically test inputs until a valid or useful response is obtained.
In short:
Although both may generate high traffic, their intent and technical mechanisms are fundamentally different.
Now that we understand the difference between brute force and DoS, it is important to recognise that brute force techniques can also indirectly impact application performance.
In some cases, applications are not properly designed to handle abusive or repetitive requests. For example, if an endpoint allows users to submit data via a POST request that creates a new entry in the system, an attacker could automate and replicate that same request thousands of times using brute force techniques. As a result, the application may accumulate a large volume of uncontrolled data.
The impact becomes visible when legitimate users attempt to access the affected section. If the application is designed to retrieve all entries in a single request — rather than implementing pagination, filtering, or query limits — the system may experience significant delays when loading the data. In extreme cases, this can degrade performance to the point where the functionality becomes unusable.
This issue is not a traditional network-level DoS attack. Instead, it is an application-layer resource abuse problem caused by poor architectural design and lack of rate limiting.
Brute force, in this context, becomes a tool to amplify design weaknesses.
Example of a brute force that affect the performance.

All of the previous examples involve attacks against live systems — whether public internet services or internal network applications. However, brute force techniques can also be performed offline, which significantly changes the risk level.
Offline brute force occurs when an attacker obtains password hashes from a compromised system, database, or internal network. A hash is not the actual password; it is a one-way cryptographic representation of it. In many cases, a hash cannot be directly used to authenticate to services. Therefore, the attacker must recover the original password by cracking the hash.
This process involves testing large numbers of candidate passwords — often using wordlists or dictionaries — and hashing each candidate until a match is found. If the computed hash matches the stolen hash, the original password has been successfully recovered.
Unlike online brute force attacks, offline cracking is not limited by rate limiting, account lockout policies, or network monitoring. The only limiting factor is computational power.
Strong, long, and complex passwords — combined with modern hashing algorithms (such as bcrypt, scrypt, or Argon2) — significantly increase the difficulty of successful cracking. However, weak passwords or poorly implemented hashing mechanisms can make recovery feasible, especially when attackers use GPU acceleration and optimised cracking tools.
Offline brute force is particularly dangerous because it moves the attack out of the defender’s visibility.
Physical and wireless technologies.
Brute force techniques are not limited to web applications, APIs, or authentication systems. Many other technologies can also be susceptible to brute force-style abuse.
For example, consider access control systems in office buildings. Have you ever noticed the card readers used to enter secure areas? These systems often rely on RFID or NFC technologies. If improperly configured, outdated, or using default credentials or weak identifiers, they may be vulnerable to repeated signal testing.
In such cases, an attacker could attempt to transmit multiple possible identifiers to the reader until a valid response is accepted. This is essentially brute forcing the identifier space of the access control system. While modern systems implement protections against this type of abuse, legacy implementations may still be exposed.
Another example involves Sub-GHz wireless communication systems used in remote controls, garage doors, IoT devices, and similar technologies. Some older or poorly designed devices rely on static or predictable signals. If signal validation mechanisms are weak, repeatedly transmitting stored or generated signals may eventually trigger a valid response.
It is important to note that modern secure systems implement rolling codes, cryptographic authentication, and replay protection mechanisms to prevent this type of brute force or replay-based abuse. However, legacy or misconfigured systems may still be vulnerable.

For web applications and APIs, it is critical to implement rate limiting across the entire host and all endpoints. Controls should be able to throttle abusive sources and, when necessary, temporarily or permanently block them within a defined time window.
In addition, layered controls should be considered, such as:
To reduce the impact of brute force and credential attacks, organisations should enforce strong authentication practices, including:
(Password expiration policies can be applied where required by policy, but modern guidance often prioritises strong passwords + MFA + monitoring over frequent forced rotation.)
Web Application Firewalls (WAF) and edge security providers can mitigate brute force and abuse before traffic reaches the application. Services such as Cloudflare, Azure Front Door WAF, or application gateway WAF solutions can help enforce:
Brute force attacks are not limited to login forms or password guessing. They can be conducted against any type of identifier or functionality and can affect many different technologies and services, including APIs, SSH, FTP, Wi-Fi networks, wireless systems, and more.
At its core, brute force is about systematically testing possibilities until a valid response is found — whether the goal is discovering credentials, enumerating resources, exhausting quotas, or abusing poorly designed functionality.
Understanding this broader definition is essential for both security professionals and developers.
Stay safe.
Be a responsible user.
Be a security-conscious developer.
And most importantly, integrate security into your development lifecycle from the very beginning, and audit your systems periodically.



